18 Oct Along the pathway to violence — correlation or causation?
The tough job in risk assessment is separating the goofiness of ordinary life from factors that might indicate potential violence. Assessment isn’t prediction — but both have similar uncertainties.
In a world with lots of physical variables, each represented by a known stochastic process the job is lots easier. A numerical simulation of the collection, such as a monte carlo analysis, can give credible results. It is even possible with data from trusted opinion polls, for example, the work of Nate Silver’s http://fivethirtyeight.com/ site.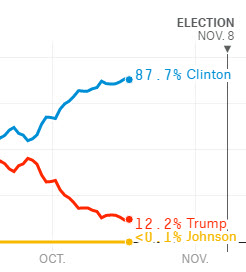
[11/9/16 update] The lesson in Silver’s colossal miss shown above is “Garbage in garbage out”. It looks like his input (polls) were just plain wrong. Data massaging is unlikely to fix bad input assumptions. Today we wonder how a 12.2% probability of success for Donald Trump could have ever been calculated weeks before the US presidential election.
Professionals in the business of threat assessment need to take the available facts to make decisions — or look for more facts. One common tool is matching current observations to items along historic pathways. These pathways rely on research, typically recognizing violence from planning to direct threats or action. Dr. Reid Meloy summarizes two other factors in his article https://www.psychologytoday.com/blog/the-forensic-files. They include fixations (focusing on something and ignoring normal activity in other areas) and violence-related identification (e.g., wanting to be like a historic serial killer).
Dr. Meloy spoke at the November 4 meeting in Seattle of the local Association of Threat Assessment Professionals chapter. http://www.atapworldwide.org/?12 His web site is http://drreidmeloy.com/
Clues that can be helpful for a threat assessment are often easily recovered from company-owned computers or cellphones. eSleuth can help in that process: https://esleuth.com/for-organizations/hr/threat-assessment/


